Okta just squashed a particularly unusual bug in its software.
The fantastic eroticism tropesdigital security management company posted a bug fix report to its website (as spotted by The Verge) letting users know that a glitch in the system that theoretically allowed bad actors to gain access to accounts had been ironed out. Sounds normal enough, right? Well, here's the kicker: The bug could've allowed someone to log into an account without entering the passwordas long as the username was 52 characters or longer.
"During specific conditions, this could allow users to authenticate by only providing the username with the stored cache key of a previous successful authentication," Okta wrote.
It should be re-emphasized that this is no longer a concern for Okta users. The bug has been fixed. Unfortunately, it existed in the system for about three months, as Okta's report said the software had been affected since July until someone noticed on Oct. 30. That's a very long time for such a vulnerability to be present, but it's unclear at this point if anyone was negatively affected by it.
Topics Cybersecurity
(Editor: {typename type="name"/})
 Amazon CEO tries to sell kids on working on the moon
Amazon CEO tries to sell kids on working on the moon
 The Morning News Roundup for April 10, 2014
The Morning News Roundup for April 10, 2014
 On Being a Regular
On Being a Regular
 Jonathan Lethem on Editing Don Carpenter’s Final Manuscript
Jonathan Lethem on Editing Don Carpenter’s Final Manuscript
 The White House might have inflated Trump's golf record, because this is how we live now
The White House might have inflated Trump's golf record, because this is how we live now
China just built the world's biggest floating solar project
 China has installed a massive field of solar panels on a particularly poignant site: a lake formed b
...[Details]
China has installed a massive field of solar panels on a particularly poignant site: a lake formed b
...[Details]
The Morning News Roundup for April 2, 2014
 Poets Want Their Privacy, and Other NewsBy Dan PiepenbringApril 2, 2014On the ShelfSmile, you’
...[Details]
Poets Want Their Privacy, and Other NewsBy Dan PiepenbringApril 2, 2014On the ShelfSmile, you’
...[Details]
How to save a GIF from X, formerly known as Twitter
 So you saw a fun GIF on X, formerly known as Twitter. That's cool, good for you, seems like fun. Now
...[Details]
So you saw a fun GIF on X, formerly known as Twitter. That's cool, good for you, seems like fun. Now
...[Details]
The Morning News Roundup for April 1, 2014
 The Circus Is Brighter in Poland, and Other NewsBy Dan PiepenbringApril 1, 2014On the Shelf“Cyrk” po
...[Details]
The Circus Is Brighter in Poland, and Other NewsBy Dan PiepenbringApril 1, 2014On the Shelf“Cyrk” po
...[Details]
Boston Celtics vs. Dallas Mavericks 2025 livestream: Watch NBA online
 TL;DR:Live stream Boston Celtics vs. Dallas Mavericks in the NBA with FuboTV, Sling TV, or YouTube T
...[Details]
TL;DR:Live stream Boston Celtics vs. Dallas Mavericks in the NBA with FuboTV, Sling TV, or YouTube T
...[Details]
The Morning News Roundup for April 11, 2014
 Kansas in Drag, and Other NewsBy Dan PiepenbringApril 11, 2014On the ShelfA photograph from Kansas C
...[Details]
Kansas in Drag, and Other NewsBy Dan PiepenbringApril 11, 2014On the ShelfA photograph from Kansas C
...[Details]
The Disappearing Face of New York by Dan Piepenbring
 The Disappearing Face of New YorkBy Dan PiepenbringApril 8, 2014LookWhat was once Optimo Cigars is n
...[Details]
The Disappearing Face of New YorkBy Dan PiepenbringApril 8, 2014LookWhat was once Optimo Cigars is n
...[Details]
William Hazlitt on Meeting Poet Samuel Taylor Coleridge
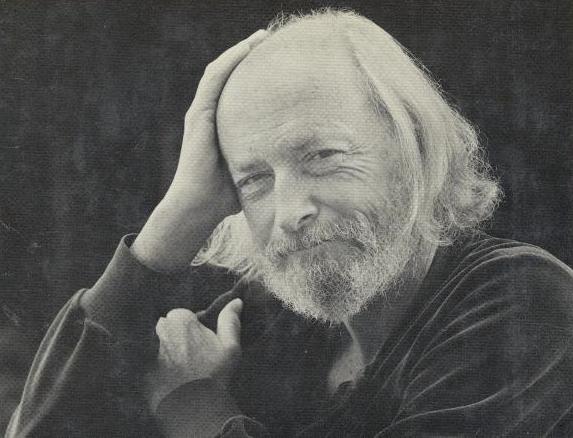
 Meeting ColeridgeBy Dan PiepenbringApril 10, 2014My Literary HeroHazlitt’s self-portrait, 1802Willia
...[Details]
Meeting ColeridgeBy Dan PiepenbringApril 10, 2014My Literary HeroHazlitt’s self-portrait, 1802Willia
...[Details]
 SAVE $200:The 14-inch M4 MacBook Pro (16GB RAM, 512GB SSD) is on sale at Best Buy for $1,399, down f
...[Details]
SAVE $200:The 14-inch M4 MacBook Pro (16GB RAM, 512GB SSD) is on sale at Best Buy for $1,399, down f
...[Details]
'Barbie': Where to buy Kate McKinnon's Weird Barbie doll
 Kate McKinnon's Weird Barbie contains multitudes. To borrow a phrase from Barbie's marketing campaig
...[Details]
Kate McKinnon's Weird Barbie contains multitudes. To borrow a phrase from Barbie's marketing campaig
...[Details]
In Paris Agreement speech, Trump never acknowledged the reality of global warming

Happy Birthday, Donald Barthelme
接受PR>=1、BR>=1,流量相当,内容相关类链接。